Unmasking the Digital Guardians: What Exactly Does a SOC Analyst Do?
In today’s interconnected world, cyber threats are a constant, evolving adversary. From sophisticated phishing schemes to large-scale data breaches, businesses and individuals face an unprecedented level of risk. But who are the unsung heroes tirelessly working behind the scenes to defend our digital lives? Enter the SOC Analyst.
You might have heard the term “SOC” thrown around in cybersecurity discussions, but what does it really mean, and what crucial role do its analysts play? This article will pull back the curtain on the world of a Security Operations Center (SOC) analyst, exploring their daily responsibilities, the skills they need, and why they are indispensable in the fight against cybercrime.

What is a SOC, Anyway? The Nerve Center of Cyber Defense
Before we delve into the analyst’s role, let’s understand the environment they operate in. A Security Operations Center (SOC) is essentially a centralized unit within an organization, staffed with cybersecurity professionals and equipped with advanced technology. Think of it as the command center for digital security, where threats are monitored, detected, analyzed, and responded to around the clock.
The primary mission of a SOC is clear: to protect the organization’s assets – data, networks, applications, and systems – from cyberattacks and ensure business continuity. It’s a proactive and reactive hub, constantly scanning the horizon for anomalies and springing into action when an incident occurs.
The Everyday Life of a SOC Analyst: More Than Just Staring at Screens
So, what does a SOC analyst do all day? It’s far from mundane, often involving intense focus, critical thinking, and rapid problem-solving. Their responsibilities can vary depending on the size and maturity of the SOC, but generally, they fall into several key areas:
1. Vigilant Monitoring and Alert Triaging
This is arguably the core function. SOC analysts spend a significant portion of their time monitoring security systems like SIEM (Security Information and Event Management) platforms, intrusion detection/prevention systems (IDS/IPS), firewalls, and endpoint detection and response (EDR) tools. These systems generate countless alerts daily. The analyst’s job is to:
- Identify legitimate threats: Differentiate between false positives and real security incidents.
- Prioritize alerts: Determine the severity and potential impact of a detected threat.
- Initial investigation: Gather initial context around an alert to decide if further action is needed.
2. Incident Detection and Analysis
When a suspicious alert is deemed legitimate, the analyst shifts into investigation mode. This involves:
- Deep diving into logs: Examining system, network, and application logs to trace the origin and scope of an attack.
- Understanding attack patterns: Recognizing common tactics, techniques, and procedures (TTPs) used by attackers.
- Using threat intelligence: Leveraging external threat feeds to identify known malicious IP addresses, domains, and malware signatures.
- Forensic analysis (often Level 2/3): For more senior analysts, this might involve deeper examination of compromised systems to understand how a breach occurred and what data was accessed.
3. Incident Response and Remediation Support
Once an incident is confirmed and analyzed, the SOC analyst plays a critical role in the response process. While specialized incident response teams might take the lead on full-scale remediation, SOC analysts are often the first responders. Their tasks include:
- Containment: Helping to isolate affected systems to prevent further spread of malware or unauthorized access.
- Coordination: Communicating findings with other cybersecurity teams, IT departments, and management.
- Remediation support: Providing crucial information that helps in patching vulnerabilities, removing malware, and restoring systems.
4. Proactive Security Measures
It’s not all reactive! SOC analysts also contribute to strengthening an organization’s overall security posture:
- Vulnerability Management: Assisting in identifying and tracking vulnerabilities within systems and applications.
- Security Tool Optimization: Fine-tuning SIEM rules, IDS/IPS signatures, and other security tools to reduce false positives and improve detection capabilities.
- Documentation and Reporting: Creating detailed reports on incidents, analyses, and security posture for internal stakeholders.
- Threat Hunting: For more advanced analysts, this involves proactively searching for undetected threats within the network, rather than waiting for an alert. This requires a deep understanding of attacker methodologies and network behavior.
5. Collaboration and Communication
Cybersecurity is a team sport. SOC analysts constantly collaborate with various teams, including:
- IT Operations: For system changes, patching, and network configurations.
- Development Teams (DevSecOps): To integrate security early into the software development lifecycle.
- Management: To report on security incidents and overall risk.
- Other Security Teams: Like GRC (Governance, Risk, and Compliance) and specialized incident responders.
The Different Tiers of SOC Analysts: A Path for Growth
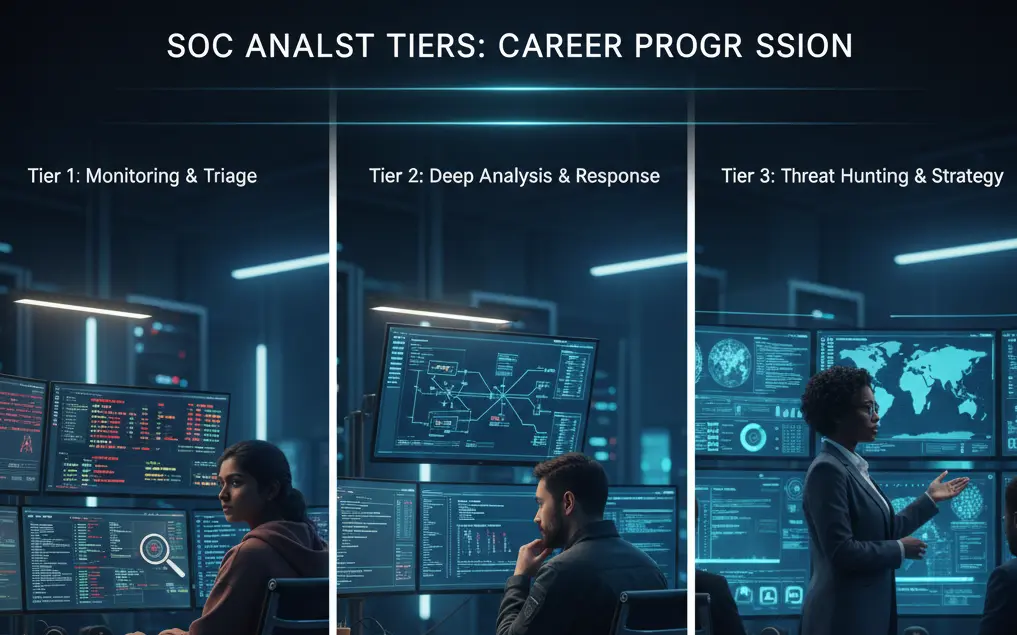
The role of a SOC analyst often comes with a clear career progression, typically categorized into tiers based on experience and expertise:
- Tier 1 (Entry-Level): These analysts are often the first line of defense. They focus on monitoring alerts, triaging basic incidents, and escalating more complex issues to higher tiers. This is a great starting point for aspiring cybersecurity professionals.
- Tier 2 (Mid-Level): With more experience, Tier 2 analysts conduct deeper investigations, perform basic forensic analysis, and contribute to incident response efforts. They are critical in reducing the workload on senior analysts.
- Tier 3 (Senior/Lead): These are the experts. Tier 3 analysts lead complex incident investigations, perform advanced threat hunting, develop new detection rules, mentor junior analysts, and often contribute to strategic security planning.
- SOC Manager: Oversees the entire SOC team, managing operations, strategy, and reporting to senior leadership.
Essential Skills for a Successful SOC Analyst
Becoming a proficient SOC analyst requires a blend of technical prowess, soft skills, and a curious mindset.
Technical Skills:
- Networking Fundamentals: A strong understanding of TCP/IP, network protocols, firewalls, and common network services.
- Operating Systems: Proficiency with Linux/Unix and Windows operating systems.
- Security Tools: Hands-on experience with SIEM platforms (Splunk, QRadar, Elastic SIEM), IDS/IPS, EDR tools, vulnerability scanners, and packet sniffers (Wireshark).
- Scripting: Basic knowledge of Python, PowerShell, or Bash for automation and data analysis.
- Threat Intelligence: Understanding how to use and interpret threat intelligence feeds.
- Cloud Security (increasingly important): Knowledge of security principles for AWS, Azure, or GCP.
- Malware Analysis (for higher tiers): Understanding how malware works and basic analysis techniques.
Soft Skills:
- Critical Thinking & Problem Solving: The ability to analyze complex situations and identify root causes.
- Attention to Detail: Meticulously examining logs and data for subtle clues.
- Communication: Clearly articulating technical information to both technical and non-technical audiences.
- Teamwork: Collaborating effectively with other security professionals and IT teams.
- Calm Under Pressure: Maintaining composure during high-stakes security incidents.
- Continuous Learning: Cybersecurity is constantly evolving, so a passion for learning is paramount.
Education and Certifications:
While a Bachelor’s degree in Computer Science, Cybersecurity, or a related field is often preferred, it’s not always a strict requirement. Many successful SOC analysts come from diverse backgrounds. What truly matters is demonstrating relevant skills and knowledge.
Valuable certifications for aspiring and current SOC analysts include:
- CompTIA Security+: A great entry-level certification covering core security concepts.
- CompTIA CySA+ (Cybersecurity Analyst): Focuses on behavioral analytics to detect, prevent, and combat cybercrime.
- (ISC)² SSCP (Systems Security Certified Practitioner): For practitioners who implement, monitor, and administer IT infrastructure.
- GIAC GCIH (GIAC Certified Incident Handler): For those involved in incident handling and response.
- Certified SOC Analyst (CSA): A specialized certification directly targeting SOC operations.
Why Are SOC Analysts So Important?
In an era where every organization is a potential target, SOC analysts are the frontline defenders safeguarding critical assets. Without them, businesses would be vulnerable to unchecked attacks, leading to:
- Financial Loss: From data breaches, ransomware payments, and operational downtime.
- Reputational Damage: Loss of customer trust and brand credibility.
- Regulatory Fines: Penalties for non-compliance with data protection laws (e.g., GDPR, CCPA).
- Operational Disruption: Business processes halted due to cyber incidents.
A skilled SOC team, led by vigilant analysts, provides peace of mind, allowing organizations to innovate and operate securely in a complex digital landscape. They are not just reacting to threats; they are actively hardening defenses and anticipating future attacks.
Joining the Ranks of Digital Guardians
The role of a SOC analyst is challenging, demanding, but incredibly rewarding. It’s a career path for those who thrive on problem-solving, have a keen eye for detail, and are passionate about protecting others in the digital realm. As cyber threats continue to evolve, the demand for skilled cybersecurity professionals, especially SOC analysts, will only grow.
If you’re looking for a dynamic career where you can make a real difference in the world of cybersecurity, becoming a SOC analyst might just be your calling. It’s a vital role that stands between our digital world and the ever-present dangers lurking in the shadows.
